A Security Operations Center (SOC) can be defined as a team of highly skilled and experienced IT security professionals that protect the organization by monitoring, detecting, analyzing, and investigating various cyber security threats. Depending on its size, each organization has a wide range of company assets that need to be protected: networks, servers, endpoints, databases, applications (in-house or in the cloud), user accounts, etc.
The SOC team, who are very often working shift patterns to achieve 24/7 coverage and are composed of multiple teams from different time zones, analyse cyber security feeds, create and modify rules for the alerts, and maintain ongoing analysis of new use cases, emerging threats, and vulnerabilities. It is a busy and engaging workplace and needs consistent efforts to be ahead of new cyber security threats.
After suspicious activity raises the alert, the SOC team investigates the potential incident by looking into surrounding events across multiple data sources, searching for additional information or indicators of compromise (IOCs) to confirm if this activity is malicious or a false positive.
If the activity is confirmed to be malicious, an incident is raised for the organization, and the SOC team follows the incident response procedures defined by the organization or the agreement between both parties.
Is there anything else to it?
- Asset Discovery and Vulnerability Management
One of the SOC team's big goals is to establish complete visibility and knowledge of the organization's assets. "You cannot protect what you cannot see," as the saying goes. By acquiring a deep awareness of all hardware, software, tools, and technologies used in the organization, the SOC ensures assets are monitored for security incidents. This is an ongoing task because the assets of the organization are in a very dynamic vast pool: new assets are added, old assets are removed, and it also extends into software or other technologies, and staying on top of emerging vulnerabilities and managing down the number of current active vulnerabilities in the organization's IT environment.
- Root Cause Investigations
If there was a confirmed true positive and an incident was declared, the SOC team would conduct root cause analysis to improve response processes and adjust detection tools if necessary. Overall, the analysis of real true-positive incidents greatly contributes to the SOC team's experience and knowledge. The SOC team continuously works on creating new incident response battlecards and playbooks and improving the current ones. This is an ongoing task, because the threat landscape is very dynamic and incident response processes need regular adjustments.
- Behavioral Monitoring
The SOC team analyzes and establishes patterns regarding human activity and behaviour around it. The biggest challenge of this task is because humans are unpredictable (it is not always a bad thing), and this poses serious security issues. We all know why phishing is the most successful and the most exploited attack vector.
- Cooperation with Threat Hunting and Threat Intelligence Teams:
These teams working in close cooperation can make a formidable SOC. Each team needs the other team, but this is a highly complex relationship and requires its own blog post..
- Compliance Management
The SOC team members must follow organizational policies, industry standards and regulatory requirements.
Where does the SIEM play a role?
Imagine you are the person responsible for an organization's cyber security and you have to investigate the user who received a malicious payload through an email attachment and clicked it. Invisible to the user, the malicious attachment disabled antivirus, downloaded a RAT (Remote Access Trojan) and started collecting users' details and sending them out to the threat actors collection server on the internet.
Your task is to collect all the evidence and establish the chain of the events that unfolded. Sounds easy, but it is not. Let us break it down:
- You have to login to email management platform and extract the logs regarding received email.
- You must extract EDR (Endpoint Detection and Response) logs, regarding activity of the malicious packages installed and activated on the user’s endpoint.
- You have to login to firewall console and extract the infected endpoint traffic to external destinations.
And this is one of the simple use cases, other cases might grow in complexity and the number of log sources needed. Also, you must compile all information based on its timestamp into reasonable sequence to have a clear picture of the story. This is a well challenging task.
What if you could access all this necessary data just through one platform? Just enter username in your search window and set the period for your search query and…magic happens. Here you can see all the activities of the user: email, endpoint, network traffic, files accessed, logins etc. I think now the importance and the ability of this tool called SIEM has become obvious.
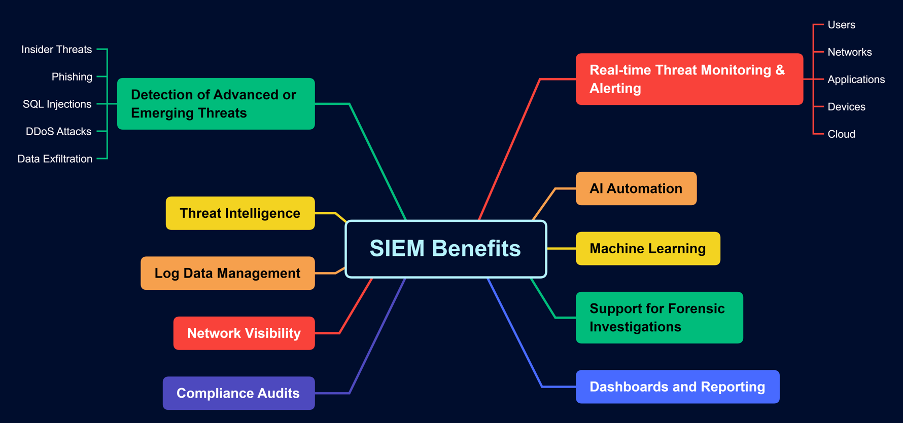
Security Information and Event Management (SIEM) is a security solution that offers real-time monitoring and analysis of events as well as tracking and logging of security data for compliance or auditing purposes.
SIEM helps to establish visibility of potential security threats and vulnerabilities before they have a chance to disrupt business operations. It expands on tracking user behavior anomalies and uses artificial intelligence to automate many of the manual processes associated with threat detection and incident response and has become a necessary tool in modern-day security operation centers for security and compliance management cases.
Today's modern SIEM integrates the power of Artificial Intelligence (AI) and Machine Learning (ML), which contribute to advanced User and Entity Behaviour Analytics (UEBA).
It is a highly efficient data orchestration system for managing ever-evolving threats as well as regulatory compliance and reporting.
The SIEM and SOC power combo
Organizations of all sizes should take proactive steps to monitor and mitigate their cyber security risks. Although SIEM technologies are amazing tools to work with whose capabilities and functions are regularly expanded and improved with the efforts and updates from SIEM vendors, we have to understand that no matter how brilliant and powerful a tool is, without the skilled people to wield it, it is worthless in improving your cybersecurity posture.