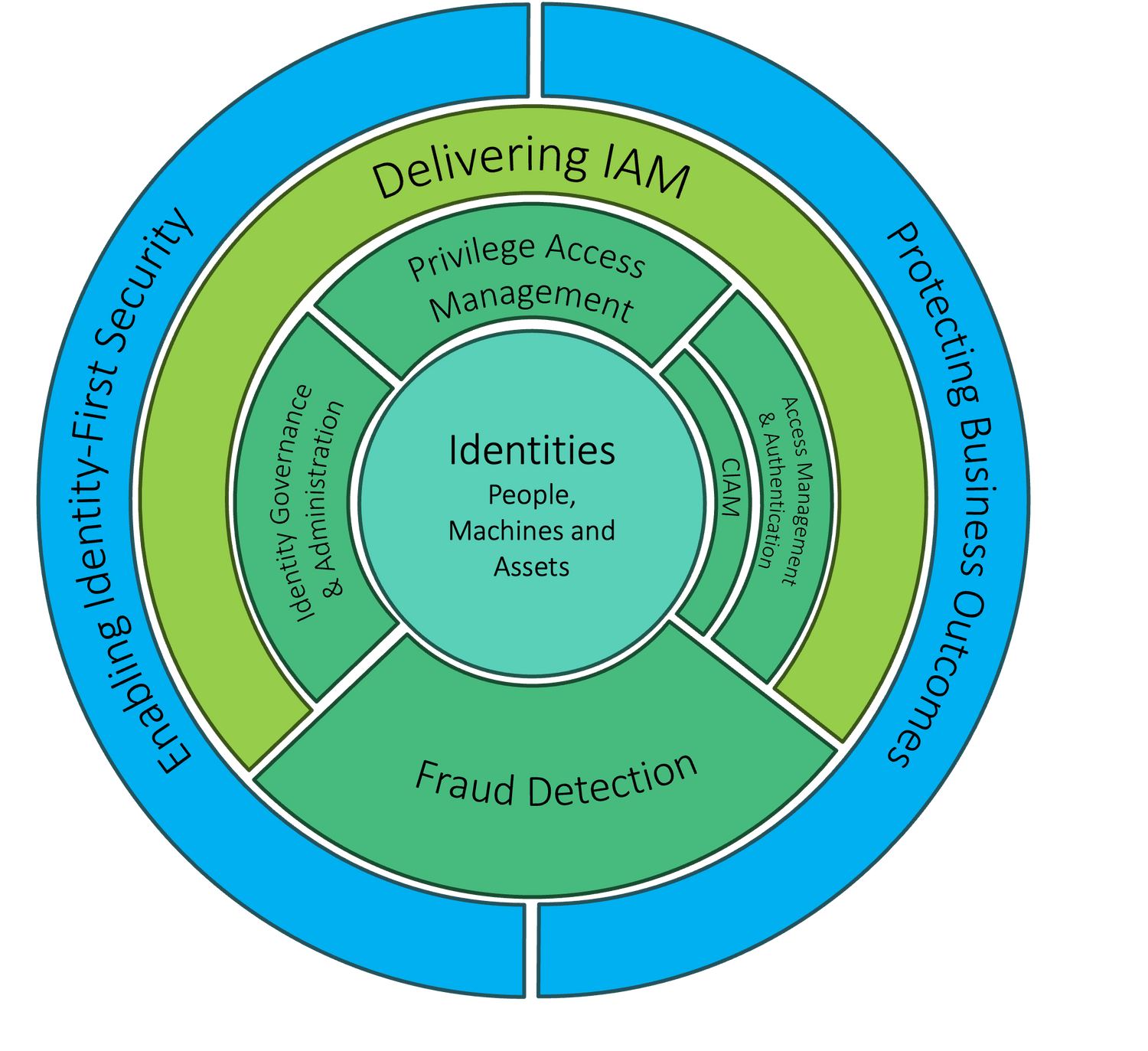
Identity centric security.
Identity Governance and Administration.
Access Management and Authentication: Verify that humans and machines are who or what they claim, and ensure that they are entitled to securely access web resources in line with zero-trust principles (via authorization and adaptive access)
Customer IAM.
Privileged Access Management: Enable secure privileged (that is, administrative) access by humans and machines by discovering, managing, brokering and logging permissions, credentials and usage.
Delivering IAM: Establish and run an effective long-term program for implementing IAM practices, processes and technologies that are aligned with business objectives.
Fraud Detection: Deploy a journey-time orchestrated stack of identity-proofing, identity-affirmation and fraud-detection capabilities to mitigate the risks of account opening and account takeover fraud while maintaining a great user experience.

Talanos will walk the path with you.
Complete Turnkey Service: Talanos can help your organisation design, plan and implement a modern IGA roadmap or let us manage and operate your PAM solution as a service.
Process Oriented: Our implementation approach involves a high degree of business process architecture and re-engineering, which we can then automate with tooling.
Ability to Execute: Highly experienced and well-trained consultants have assisted various customers globally through their IGA and PAM implementations.
Change Management: After many successful projects, customers regularly cite our focus on change management and communication as key to our shared success.
Get control of your privileged accounts, contact one of our principal identity consultants.

We're working to embed our values into everything we do and our customers notice:
No surprises!
- Transparent pricing, no hidden costs and focused on measurable ROI.
- Streamlined and flexible contracting, ensuring ease of doing business.
Talented People.
- Exceptional people backed by robust security and quality delivery systems (ISO 27001 and ISO 9001 accredited).
- Passionate about cyber, demonstrated by industry-leading certifications and groundbreaking research.
Always There. Always Caring.
- Named analysts who become an extension of your team, offering expert advice and proactive recommendations.
- Global 24/7 team delivering resilience and diverse thinking, supported by regional teams for the local touch.