Certified and Accredited
Highly rated by our customers on Gartner Peer Insights.
A high touch service.
The Talanos team of engineers, lead analysts, threat intelligence experts and dedicated service manager will regularly meet with your team to build strong relationships and develop a deep understanding of your business.
- Personalised reporting presented and discussed using business-friendly language in service reviews.
- Focus on detected weaknesses (through pattern analysis, incident review and customer feedback) as inputs into the threat models that inform the IT risk management process.
- Relevant threat intelligence and external risks discussed to shape the overall cyber strategy.
- Measure the efficacy of deployed security controls to guide cyber spending.
- Opportunities for service extension and security posture improvement are discussed based on collected evidence.

Our team is your team.
Your 24/7 team will be composed of at least 7 named analysts supported by dedicated security engineering, security operations, incident responders, threat intelligence experts and service managers. Each of your Talanos team members will:
- Have an average of 8 cybersecurity and IT related qualifications.
- Have an average of 7 years' experience with Talanos in their specific security role.
- Speak multiple languages as well as English.
- Spend a third of their time researching the latest threats and developing their skills on our training platforms.
Is an MDR / SOC service the right fit for you?
-
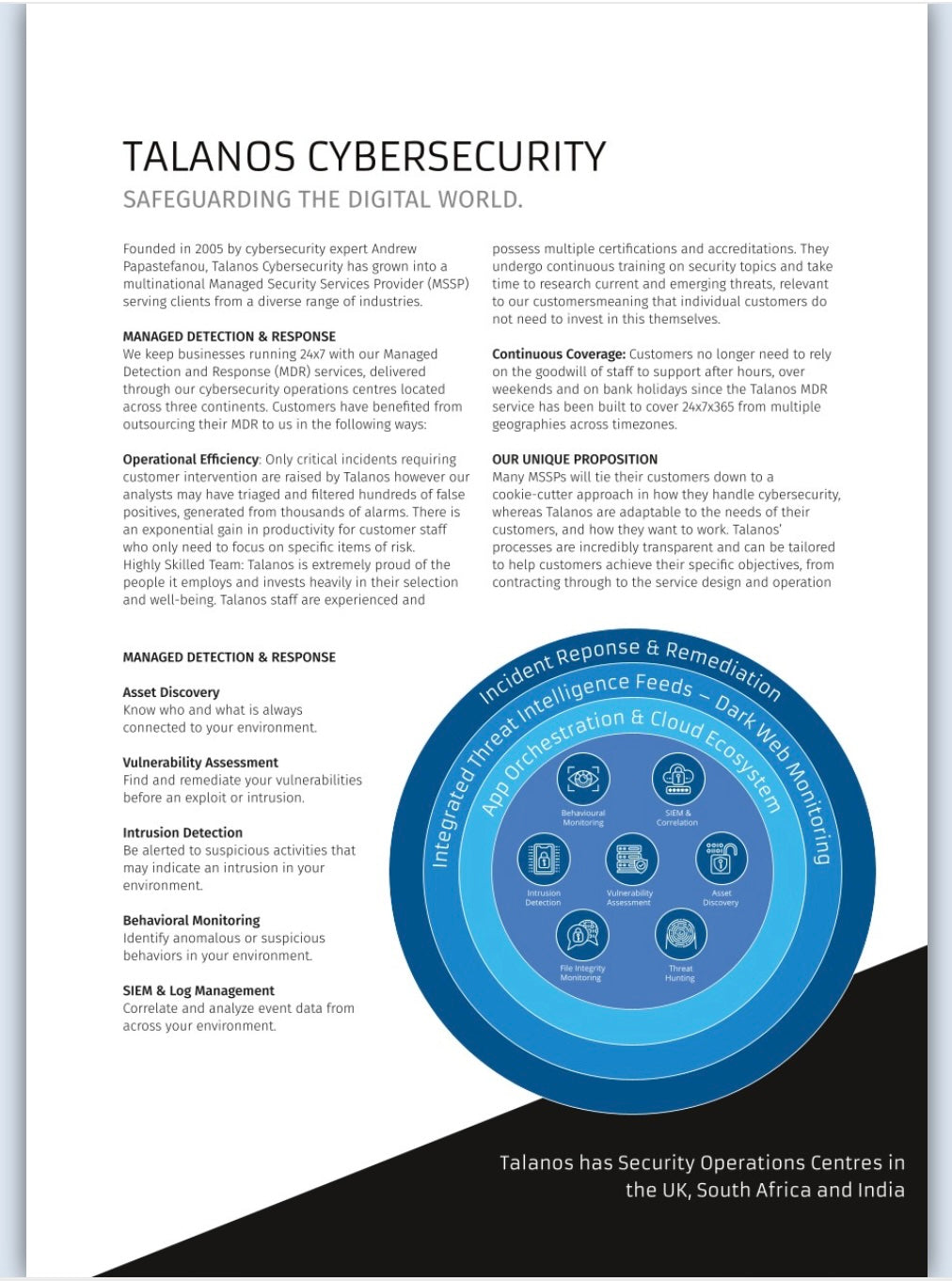
Managed EDR
Managed EDRModern Endpoint Detection and Response tools such as Microsoft Defender, SentinelOne, CrowdStrike and even DarkTrace generate a huge amount of data in the form of events and alerts. Managing these tools as well as understanding the data they generate is a daunting task for many smaller IT teams.
With the Talanos Managed EDR solution, your chosen platform will be optimally configured and monitored 24/7 to detect and respond to threats.
-
Managed SIEM / XDR
Managed SIEM / XDRCombining security information from the organisation's EDR, network infrastructure and critical applications whether they are on-premise, SaaS or in the cloud, enables comprehensive detection of threats based on their behaviours throughout the entire IT environment. Combined with automation and orchestration, critical and time sensitive containment actions can be triggered across a number of the organisations tools.
The Talanos Managed SIEM / XDR solution will provide the organisation with a strong engineering team to build and maintain a detection capability on your chosen platform, monitor it 24/7 and respond to threats.
MDR Solution Brief
Download a whitepaper that describes how our MDR service helps organisations reduce their cyber risk and boost their operational efficiency.
Read what customers have to say about the value of our human lead, 24x7 protection that keeps their businesses running.
Get peace of mind and speak with one of our security advisors.

We're working to embed our values into everything we do and our customers notice:
No surprises!
- Transparent pricing, no hidden costs and focused on measurable ROI.
- Streamlined and flexible contracting, ensuring ease of doing business.
Talented People.
- Exceptional people backed by robust security and quality delivery systems (ISO 27001 and ISO 9001 accredited).
- Passionate about cyber, demonstrated by industry-leading certifications and groundbreaking research.
Always There. Always Caring.
- Named analysts who become an extension of your team, offering expert advice and proactive recommendations.
- Global 24/7 team delivering resilience and diverse thinking, supported by regional teams for the local touch.
Questions
Frequently Asked Questions
What are Talanos' SLAs?
What are Talanos' SLAs?
Talanos runs a 24/7/365 incident response service and therefore all security events are triaged within 15 minutes and highest priority incidents are contained within an hour. Talanos works with our customers to agree the categorisation and prioritisation matrix (with associated SLAs and definitions) during the service management design phase of the onboarding project.
Do Talanos take their own cybersecurity seriously?
Do Talanos take their own cybersecurity seriously?
Yes. Not only are Talanos ISO 27001 and ISO 9001 certified but we have also maintained our Cyber Essentials Plus certification for many years which includes testing of our various security controls. Controls not covered by any of the above frameworks, are maturity assessed against NIST CSF v2.0 with further guidance from NIST 800-53 rev 5 and customers may request our security maturity assessments after completing an NDA.
What levels of insurance do Talanos have in place?
What levels of insurance do Talanos have in place?
At the customer's reasonable request, Talanos may adjust it's insurance levels to meet any requirement:
- Professional indemnity insurance: £2,000,000
- Employer’s liability insurance: £10,000,000
- Public liability insurance: £5,000,000





